The Importance of Software Supply Chain Security- Insights from the 2024 DBIR Report
The 2024 Verizon DBIR reveals a sharp increase in software supply chain attacks. Discover why securing your software supply chain is crucial, learn about high-profile incidents, and explore strategic measures to mitigate these escalating threats. Stay informed and protect your organization against vulnerabilities and sophisticated cyber adversaries.

Introduction
The 2024 Verizon Data Breach Investigations Report (DBIR) highlights a stark reality: software supply chain attacks are rapidly escalating. These attacks are not just theoretical concerns. They are actively disrupting industries and compromising sensitive data worldwide.
As these threats grow in frequency and sophistication, the need for organizations to bolster their software supply chain defenses becomes increasingly urgent.
The real-world application of C-SCRM is demonstrated in our Department of the Interior C-SCRM case study, where a structured program was built at federal scale to manage risks across a complex supplier base.
The NIST SP 800-161 guidelines provide the authoritative technical framework for C-SCRM, defining the specific practices that federal agencies and their suppliers must implement to meet supply chain security requirements.
Organizations new to the discipline should start with a clear understanding of what C-SCRM is and why it matters before building program components. The foundational concepts define what risks you are actually managing.
The Escalating Threat Environment
The 2024 DBIR reveals a staggering 68% increase in supply chain interconnection-related breaches, jumping from 9% to 15% of all analyzed breaches. This surge highlights a critical vulnerability: third-party software.
These vulnerabilities are frequently exploited, creating severe ripple effects across various sectors. The sophistication and frequency of these attacks signal a pressing need for more stringent security measures.
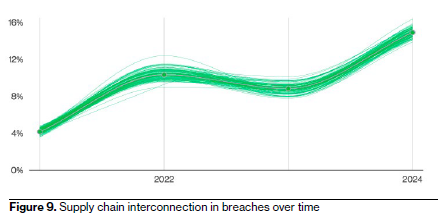
This diagram illustrates the significant increase in breaches involving third-party connections, emphasizing the urgent need for strong software supply chain security measures. Credits: Verizon DBIR 2024
As businesses become more interconnected, the attack surface expands, making it easier for cybercriminals to infiltrate networks through less secure third-party applications. This trend underscores the importance of thorough risk assessments and continuous monitoring of all software components within an organization's environment.
High-Profile Incidents as a Wake-Up Call
High-profile incidents like the 3CX supply chain attack serve as a sobering reminder of the sophisticated capabilities of cyber adversaries. In this attack, North Korean APT actors, specifically the Lazarus Group, infiltrated the software development process of 3CX, distributing a trojanized VoIP desktop client to numerous customers worldwide.
This meticulously planned attack targeted cryptocurrency companies, demonstrating the precision with which modern cyber threats can be executed.
Such incidents highlight the need for rigorous vetting of software vendors and the implementation of advanced threat detection mechanisms. Regular audits and penetration testing can help identify vulnerabilities before they are exploited by malicious actors.
The MOVEit Debacle, a Case Study in Vulnerability Exploitation
The MOVEit incident stands out as an example of the catastrophic impact of unpatched vulnerabilities in third-party software. This breach, which exploited a zero-day vulnerability in managed file transfer software, affected over 1,000 organizations and compromised the personal information of at least 100 million individuals.
The MOVEit breach is a glaring illustration of how a single vulnerability can cascade through an entire supply chain, particularly affecting the education sector.
This incident underscores the necessity for timely patch management and the importance of maintaining an updated inventory of all software assets. Implementing automated patch management solutions can significantly reduce the window of exposure to such vulnerabilities.
Strategic Mitigation Measures
To combat these threats, the 2024 DBIR offers a suite of strategic recommendations:
- Implementing Secure Configuration Processes: Establishing and maintaining secure configurations for enterprise assets and network infrastructure is foundational, significantly reducing potential entry points for attackers. Organizations should adopt industry best practices and frameworks such as CIS Controls or NIST SP 800-53 to guide their configuration management efforts. Regularly reviewing and updating these configurations is essential to address evolving threats and vulnerabilities.
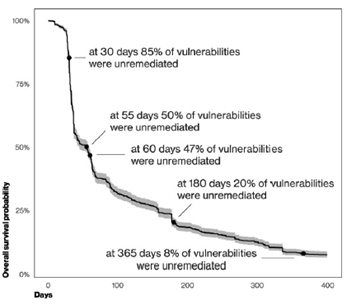
- Continuous Vulnerability Management: The DBIR notes a critical insight: once patches are available, it typically takes about 55 days to remediate 50% of critical vulnerabilities, highlighting the need for swift action. The patching doesn’t seem to start picking up until after the 30-day mark, and by the end of a whole year, around 8% of them are still open. Organizations should develop and maintain strong processes to identify and remediate vulnerabilities promptly. Incorporating vulnerability scanning tools and prioritizing remediation efforts based on the severity and exploitability of vulnerabilities can enhance an organization's security posture. Engaging in threat intelligence sharing with industry peers can also provide valuable insights into emerging threats and vulnerabilities.
- Adopting Secure Software Development Practices: The "secure by design" approach integrates security measures throughout the software development lifecycle, ensuring resilience against attacks. This includes incorporating security testing at each phase of development, from initial design to final deployment. The DBIR suggests reviewing in-depth reports like the CISA's "Secure by Design" to understand and implement best practices and buyer expectations. Adopting DevSecOps practices can further embed security into the development process, fostering a culture of continuous improvement and vigilance.
- Ensuring Supply Chain Accountability: Holding software vendors accountable is essential for ensuring supply chain security. This involves ensuring that vendors adhere to secure development practices and promptly address vulnerabilities. Expanding third-party involvement metrics to include the exploitation of vulnerabilities, as highlighted in the DBIR, can help organizations make more informed decisions when selecting vendors. Establishing clear contractual obligations for security practices and conducting regular security assessments of third-party vendors can mitigate risks associated with external dependencies.
- The Human Element: A Double-Edged Sword: The human element remains a significant factor in supply chain security. The DBIR reveals that more than two-thirds of breaches involve human aspects, whether through errors, misuse, or social engineering attacks. This statistic underscores the necessity of investing in thorough security awareness and training programs to mitigate risks associated with human errors and insider threats. Encouraging a security-conscious culture within the organization, where employees are vigilant and knowledgeable about potential threats, can significantly reduce the likelihood of successful attacks. Regular phishing simulations and interactive training sessions can enhance employees' ability to recognize and respond to suspicious activities.
Final Thoughts on the Future of Software Supply Chain Security
The insights from the 2024 DBIR are a clarion call for organizations to enhance their software supply chain security. Understanding the trends and implementing strong security measures are not optional. They are imperative.
By focusing on secure configurations, continuous vulnerability management, secure software development, and holding vendors accountable, organizations can significantly bolster their defenses against supply chain attacks.
As cyber threats continue to evolve, staying informed and proactive is essential. The detailed findings of the 2024 DBIR provide a roadmap for organizations to fortify their defenses and protect their critical assets from the ever-growing threat of software supply chain attacks.
Embracing an end-to-end approach to cybersecurity, which includes technological solutions, process improvements, and human-centric strategies, will enable organizations to work through the complex threat environment and secure their digital future.
